A brief context
- This project concerns a large multi-cloud customer: more than 10,000 employees
- Who has an AWS landing-zone automation: 30 -> 600 AWS accounts in 3 years
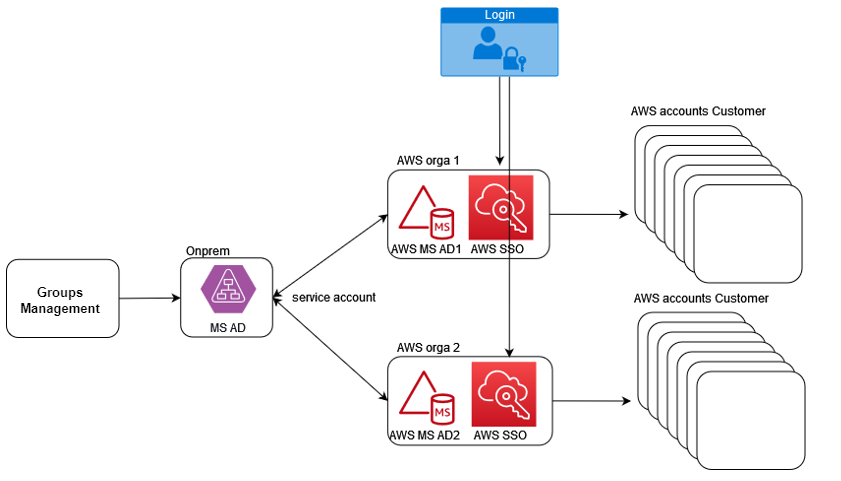
- And several AWS Organizations
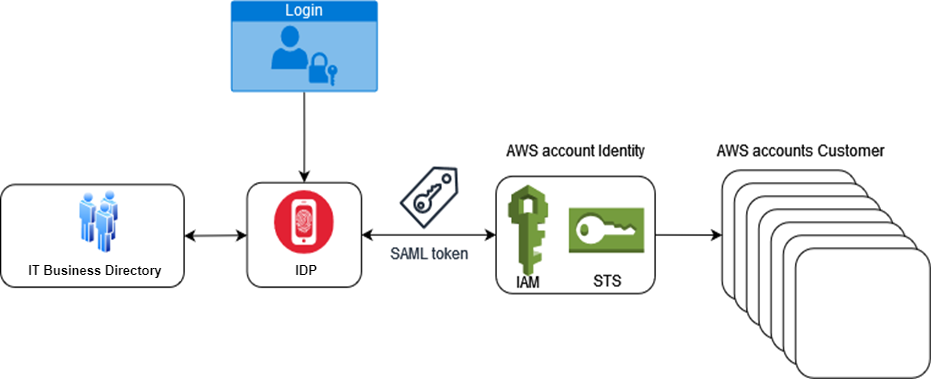
Customer AWS access, whether human or programmatic, relied on centralizing all connections through a single AWS account ‘Identity’.
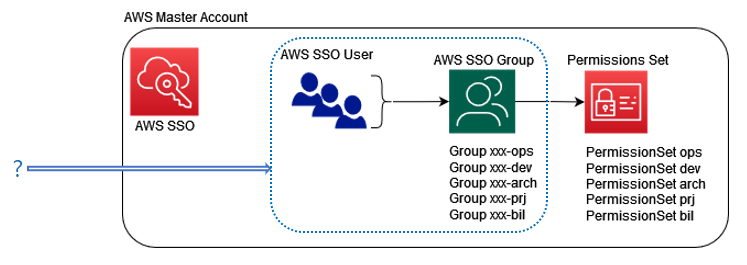
The hard limit of ‘5000 roles/AWS account’ launched the SSO project (aka IAM Identity Center).
The SSO Project:
Target
- Manage AWS console access for projects on their dedicated AWS accounts
Cross-functional access and IAC remain on the Identity model so as not to overload AWS IAM Identity Center, which has API limits to consider.
Constraints
- Implement security: corporated MFA and source IP restriction
- Be scalable: up to 10,000 users
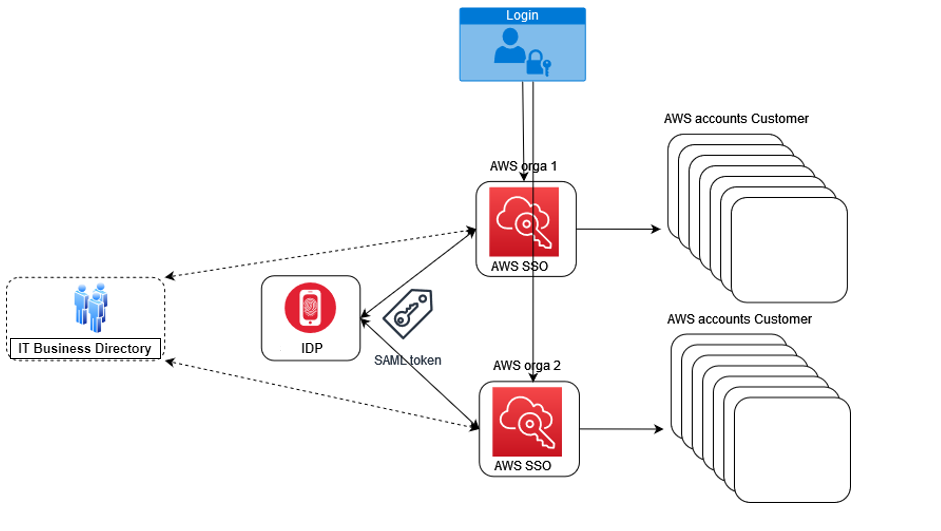
- Manage segmentation between multi AWS organizations
The question
- What to populate the AWS SSO directory with ?
The answers
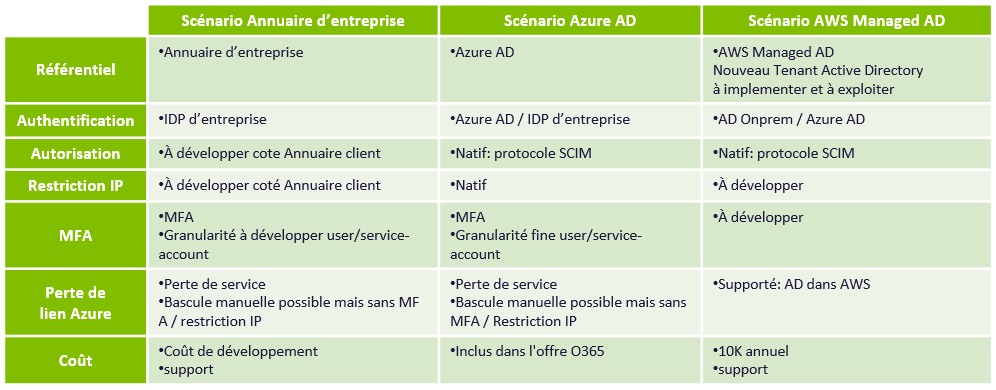
Several sources can be proposed because the customer has differents Active Directories, and the analysis of interest will be made according to the specificities of each.
- AWS SSO and customer directory:
This solution does not change the customer referential and procedures, but requires development of functionalities, such as synchroni
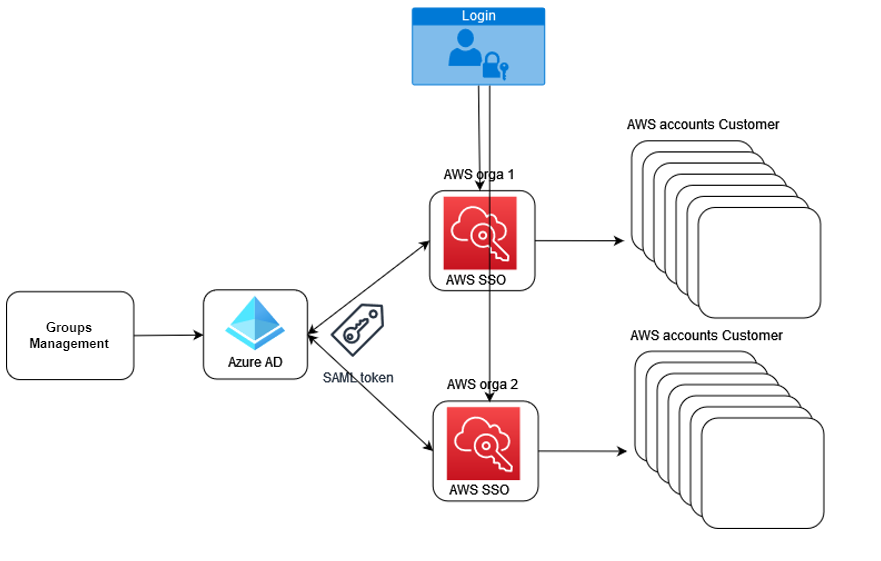
- AWS SSO and Azure AD :
This solution natively integrates the most features: MFA management and restriction of source IPs with Azure Conditionnal Access and SCIM synchronization with AWS SSO. Its main flaw is to create a dependency between AWS and Azure.
- AWS SSO and AD Onprem :
This solution involves the use of the AWS Managed AD service. Its interest is to support by-design link failure. Its default is to impose the management of a new Tenant AD to the customer.
Review
The choice
The use of Azure AD was established after having been debated by various decision-making committees of the customer, helped by the SAAS culture of the company.
Next
After this survey, the architecture and automation of SSO accesses will be discussed in sections 2/3 and 3/3 of this story.
We will discuss logical roles management for such a quantity and various technical constraints such as synchronization between Azure and AWS as well as handling some limits of SSO API calls.
Paul Boucher, Team Leader AWS